Ridgeback Network Defence
Disrupt and eliminate hackers before they succeed.
Ridgeback is a unique, modern solution to protect your network from lateral threats. We are a true network defence solution that operates at its core, protecting your data in real time.

Traditional security is failing enterprises to secure themselves.
After an attacker has gained an initial foothold in a network, they look to broaden and cement further control over your endpoints, data and systems. This activity is known as lateral movement.
Ridgeback stops lateral movement by disrupting network discovery by attackers and eliminates them before they can succeed.
Almost all types of cyber-attacks involve some kind of lateral movement. Yet, the lateral movement remains undetected by nearly all cybersecurity products.
When it comes to boundaryless enterprises and interconnected systems, omnichannel business operations demand secured, highly accessible platforms. With thousands of malware released daily, one breach can erode an organisation’s operating ability, customer credibility and sustainability.
A firewall, antivirus or any other signature-scan-based defence is incapable to defend or stop the attack.
Modern hacking is driven by sophisticated deceiving technologies. Phishing, zero-day, malicious content-based attacks can filter through firewalls and antivirus systems without being detected. Your enterprise can no longer rely upon these end-point protection technologies.
Ridgeback is the only lateral threat defence solution that neutralises hackers and other malicious intruders who have infiltrated your network in real-time, without generating false positives.
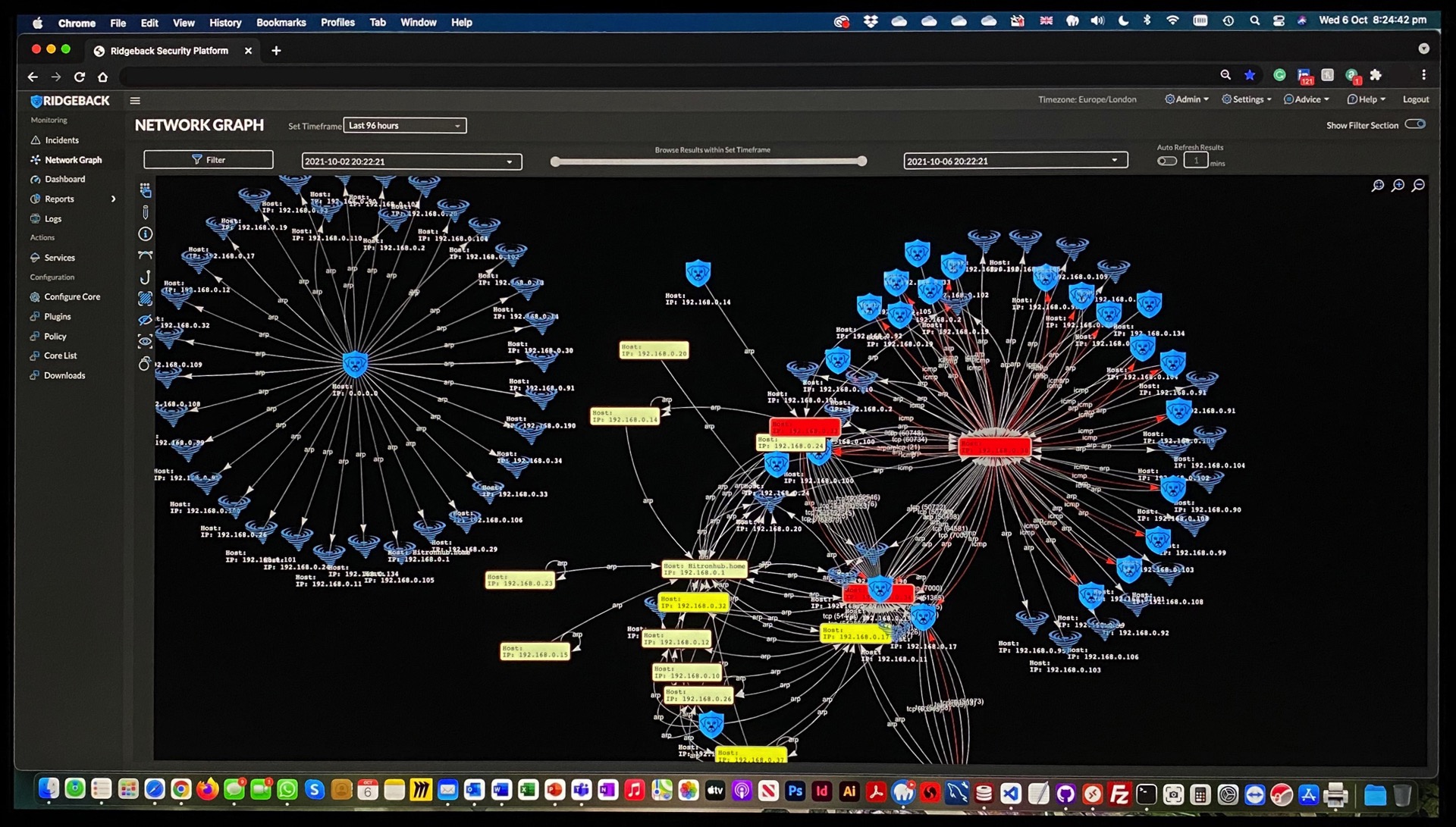
The Ridgeback solution scans through all your network endpoints and protects your network by monitoring and scanning your network behaviour in real time, both in a physical and virtual sense.
With sophisticated detection and prevention technology, Ridgeback is the easiest solution to deploy; starting work from the moment it is powered on by analysing your network and your device behaviours. Armed with a simple user interface and reporting capability, you can monitor your network from ‘inside’ as it functions.
Real-time Lateral Threat Protection
Simple Agent-less Deployment
Zero Performance Impact
Automated and Scalable
Multi-tenant Capability
No False Positives
You need Ridgeback today and now!
Send us a message and we will demo the powerful capabilities of Ridgeback. We can also conduct a pilot deployment for you to appreciate its threat neutralisation capabilities, giving your enterprise’s security model a much-needed uplift.
